






Transform agent productivity and create happier customers with our unified customer service, chat, and helpdesk platform with built-in AI.
14-day free trial. No credit card required.
Re:amaze helps amazing companies deliver better customer service and customer engagement.














Consolidate all your customer support channels and respond faster than ever before.
INTELLIGENT CUSTOMER HELPDESK
Re:amaze combines email, AI-powered live chat, social media, mobile SMS, VoIP, video calls, and push notification conversations seamlessly so your support team can focus on creating amazing customer experiences. Collaborate with teammates using assignments, notes, and shared views.
Automate common tasks using a combination of workflow macros and AI to create professional and delightful customer experiences that drive repeat customers and higher satisfaction.

Jeff Newman
Co-Founder and
CMO at BuiltBar
The difference between what we had before Re:amaze and now has been incredible. Re:amaze has truly reinvented our customer service model, and in amazing ways.
Read Case Study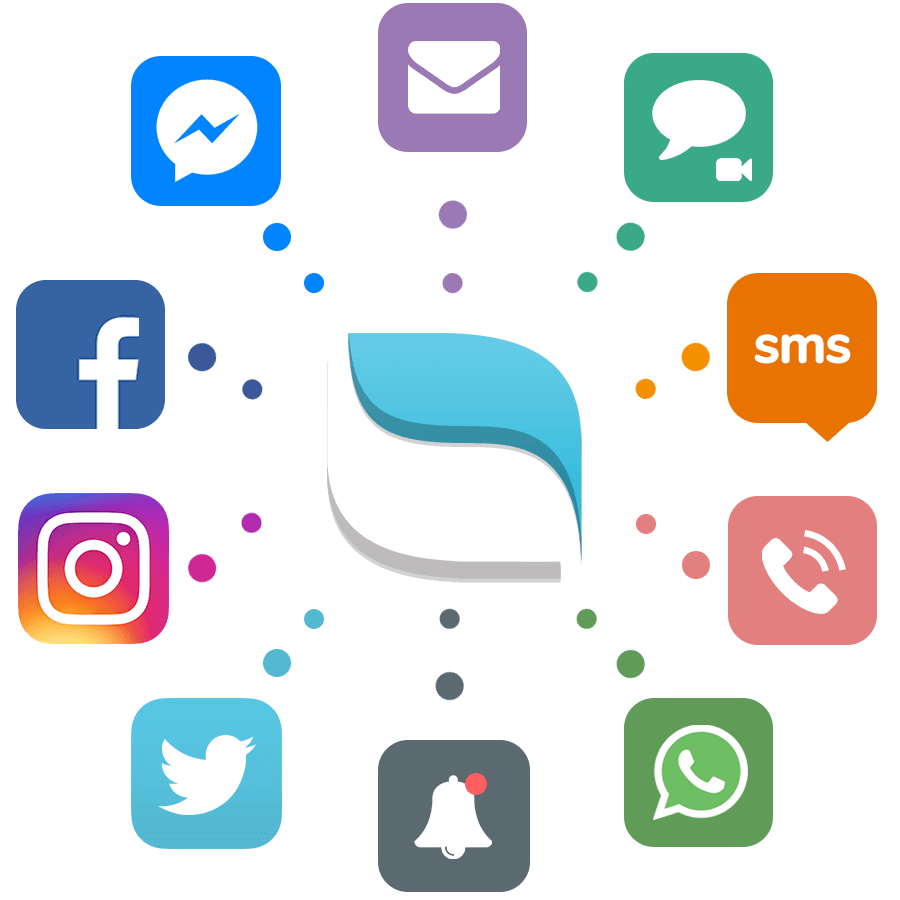
Let AI handle your chats
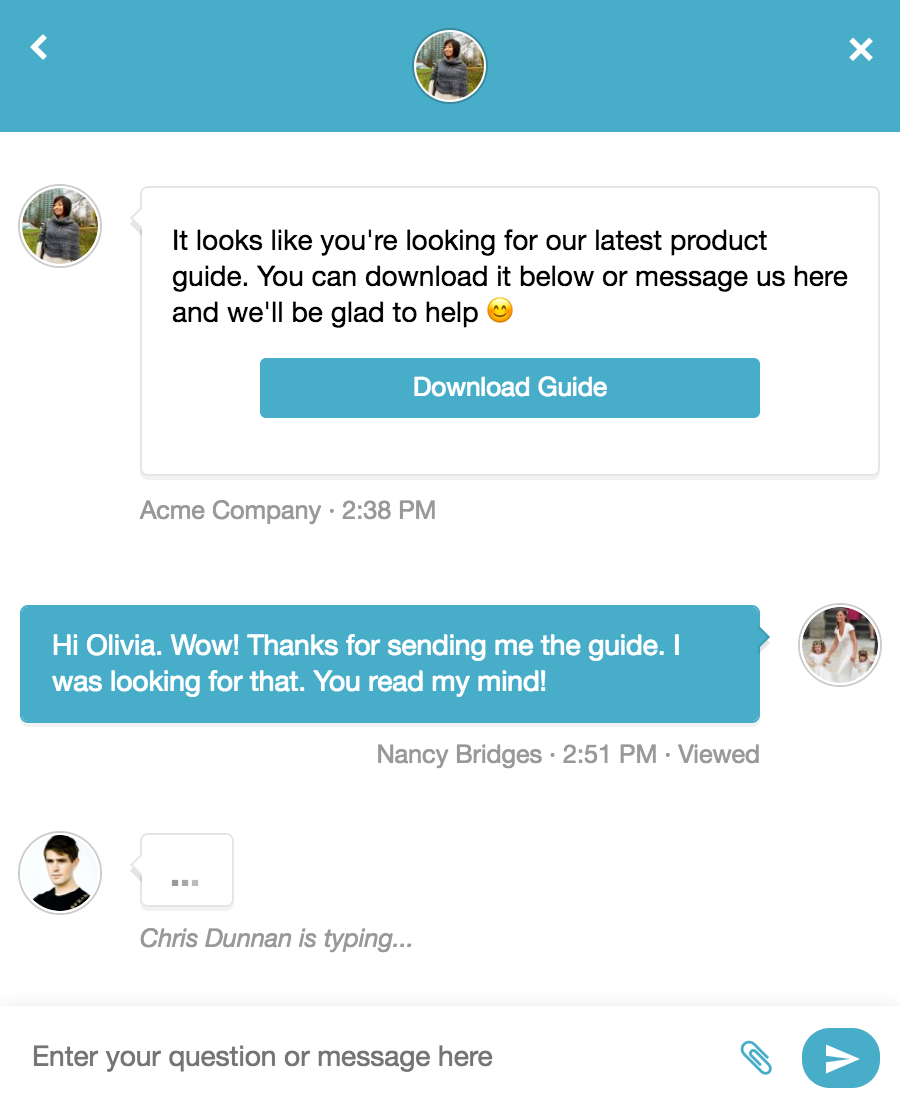
Smart engagement
Send automated and targeted AI-generated messages to customers on your website for better engagement using Cues.
Autopilot for chat
Re:amaze AI Agent (Beta) is your new 24/7 assistant. Train your AI Agent with details about your business and start delivering efficient, personalized support at a fraction of the cost.
Co-browse with AI
Watch how AI is responding while you deep dive into research using Peek to see customer behavior in real time. See how customers are planning to reply before they even hit send.

Olga
Animatron
What we love about Reamaze is the fact that it helps us provide better support to our customers. It's easy to keep track of the conversations that our team is involved in and give timely replies to all the questions. Without Reamaze, it would be cumbersome to manage all our communication channels.
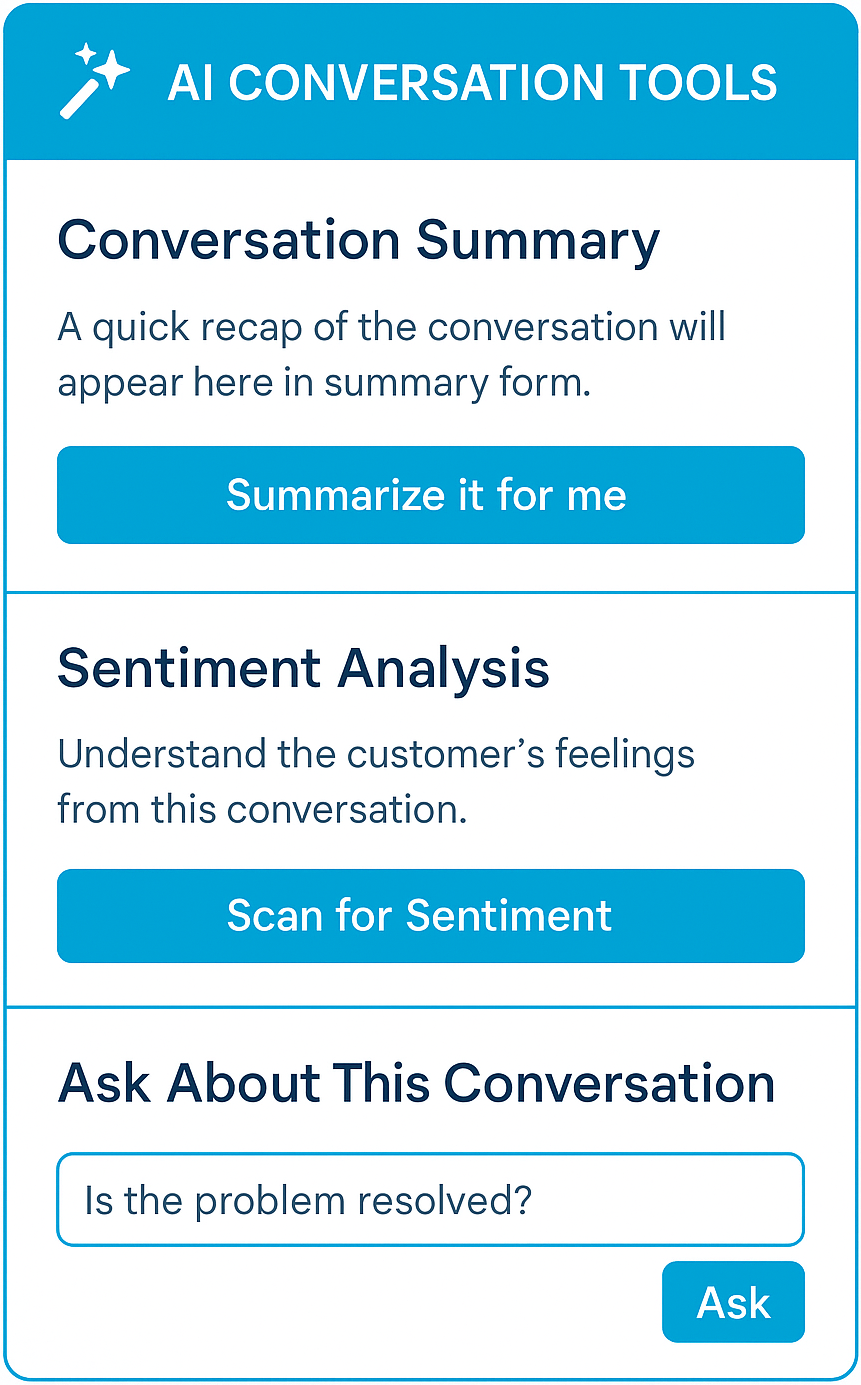
Upgrade your customer support with AI-powered tools and insights
AI-powered support for faster answers
Help customers find answers faster with AI-powered suggestions and article creation. AI can automatically suggest relevant FAQs, assist in drafting new articles, and analyze conversations to provide useful insights.
Smart conversations with AI assistance
Let AI assist with pre-drafting customer replies, summarize long conversations, and gauge sentiment to improve response quality. With AI handling repetitive tasks, your team can focus on more complex inquires.
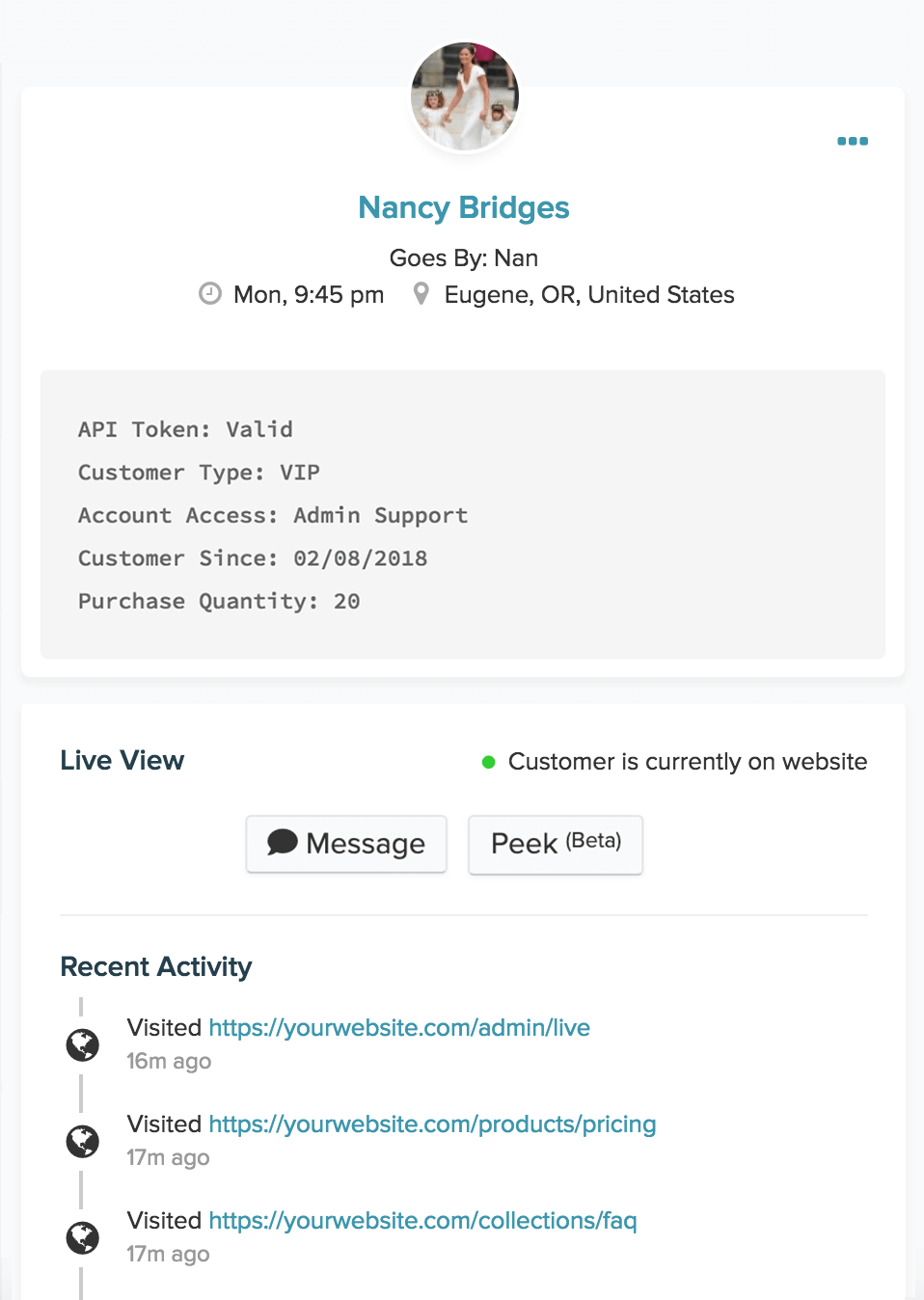
Know your customers. Empower your team with real time customer data
Live Dashboard
Monitor customers’ browsing activity, shopping data, and geolocation on your site and message them directly.
Connected customer insights
View custom profile data about your customers when they message your team. Automatically pull data from 3rd party apps or integrate your own app data via our SDK. Use AI to instantly scan for conversation sentiment and generate concise summaries, ensuring agents have the complete context at a glance.

Davis
Printful
We’ve grown with Reamaze from just 1 operator to almost 30 now. We joined because of the simplicity and stayed for how they continue to execute on new stuff.
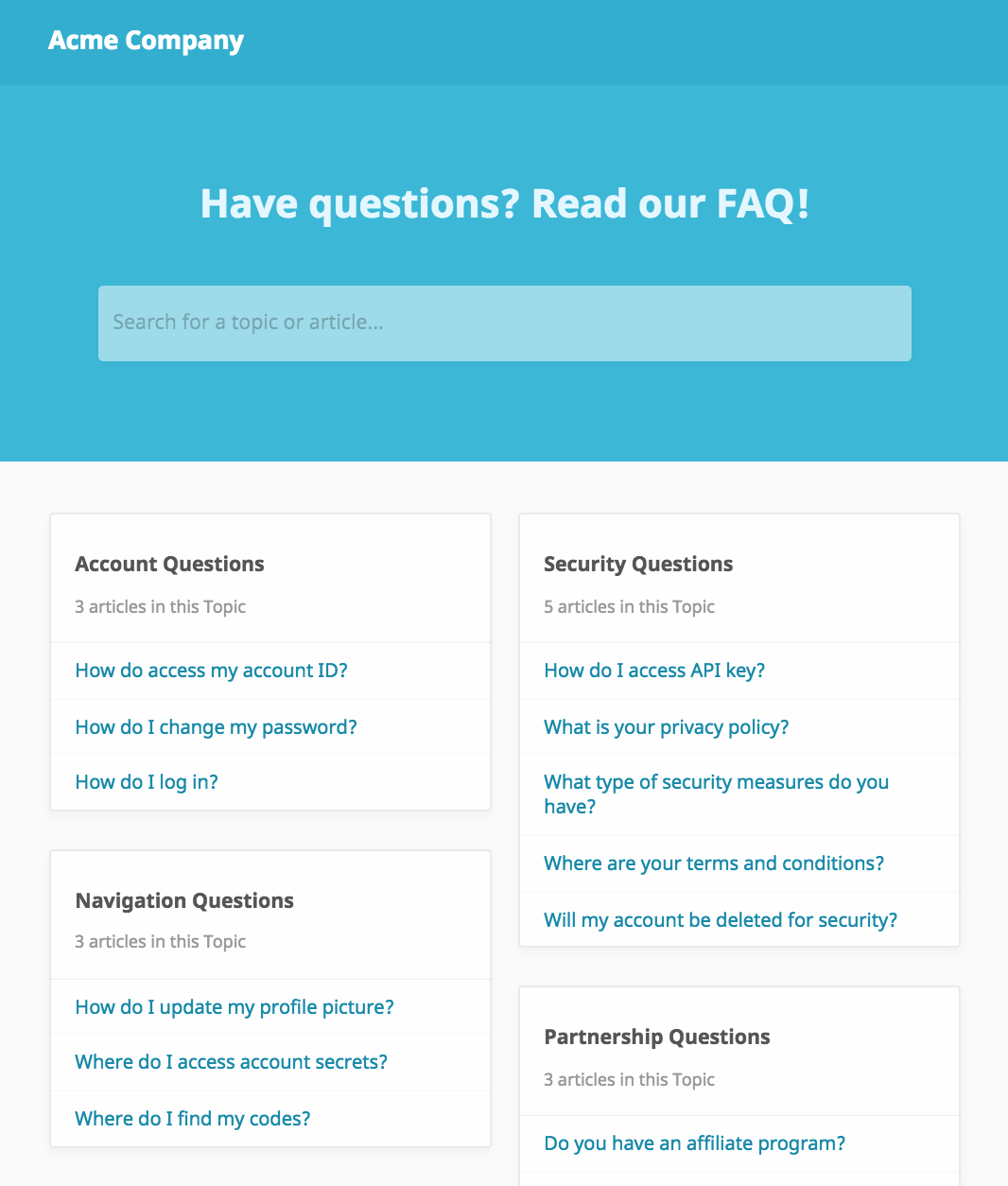
Help Center and FAQ that trains your AI Agent
AI Knowledge Base
Articles created acts as a repository of knowledge that trains your AI Agent and chatbots. Updates made are added as context instantly. No complex workflows or training needed.
Customizable and branded for your business
Offer your customers organized self-service support with rich topics and articles. Drastically reduce content creation time with AI-powered article generation, giving you instant drafts to refine and publish.
Embeddable or Self-Hosted
Your FAQ can be displayed as a Help Site on the domain of your choice, embedded inline on your existing website or displayed within Chat.

Adam
Ellusionist
Reamaze has fundamentally changed how we interact with our customers and the speed with which we support them. It offers us central place to track all customer issues and inquiries and the tight integration with all of our existing systems had us up and running in a matter of minutes.
All the bells and whistles to impress customers.
Re:amaze is loaded with awesome features to help you succeed.
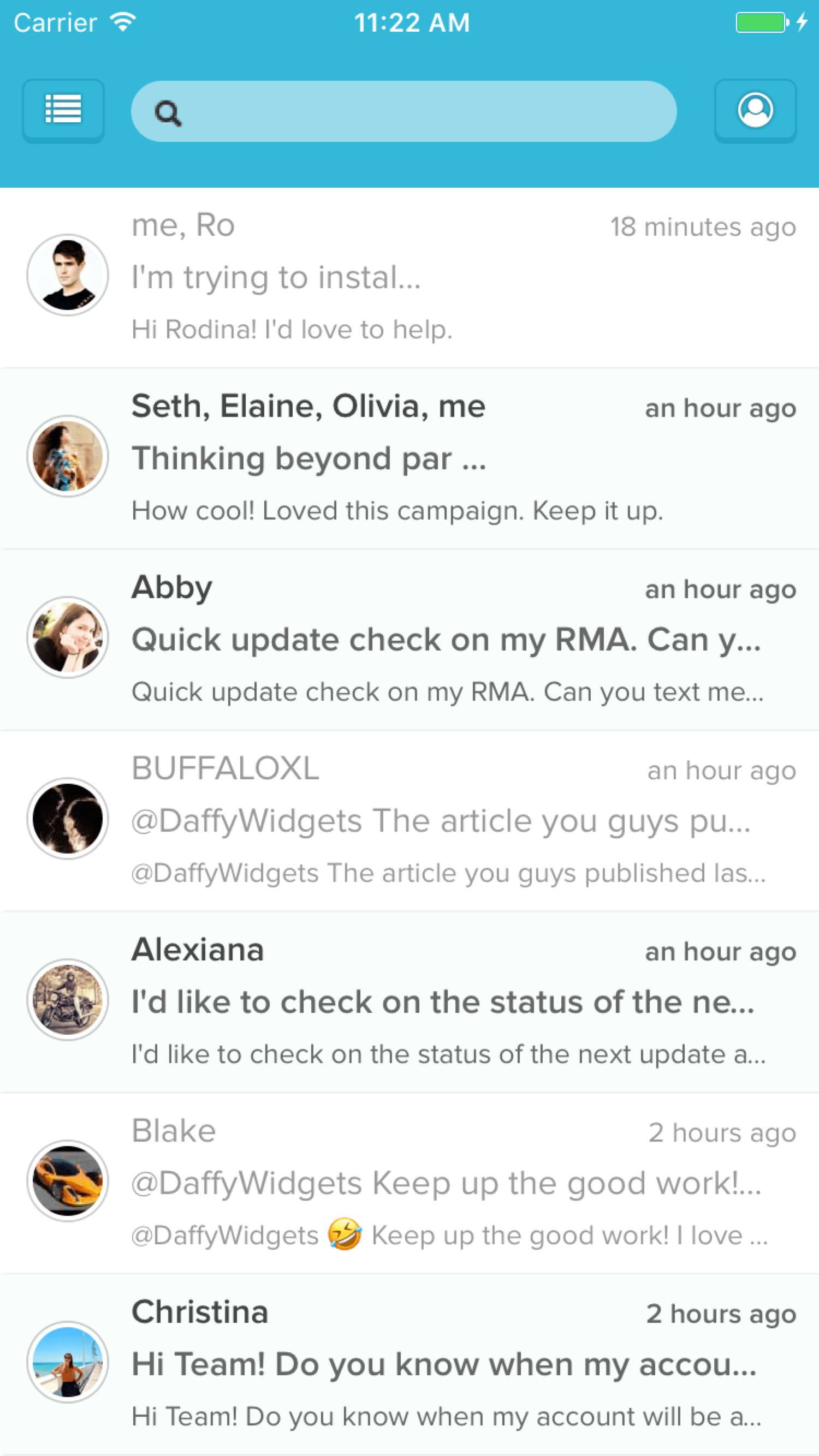
Re:amaze Mobile helps you keep customers close while on the go.
Available on iOS and Android
Re:amaze is mobile ready for your team so you can always impress customers with a few taps. Download our mobile apps and receive push notifications for direct messaging with customers while you're on the go.
Integrate your favorite apps to keep your team running in sync and on point.
Unite your team
Got a unique workflow? We've got an app for that. Reamaze works with the tools your team already loves so you don't have to change. Simply connect and bring Reamaze with you.
Build your own
Integrate with your own data backend by building a custom data module within your support dashboard.

Kat
Moviepilot
In order to optimize communication with over 30 million fans, we required a tool which would seamlessly integrate all of our channels into one manageable interface. Reamaze solved that problem for us.
Let's get started
Start with the 14 Days Free Trial, then you will be able to pick a plan in your account settings.
Still unsure?
Contact our support team to get more details. We're happy to simplify things even more.
Join thousands of teams using Reamaze to impress customers.
Find out how with a free account.


